Enjoy a comfortable sense of security; a false one, though

“Apple to let you sign up for services with Face/Touch ID instead of passwords” https://mashable.com/article/apple-passkeys/?
It reads "In a WWDC developer session titled "Move beyond passwords," Apple engineer Garret Davidson shows a new feature, allowing users to sign up for new online services using Face ID or Touch ID instead of a password. "
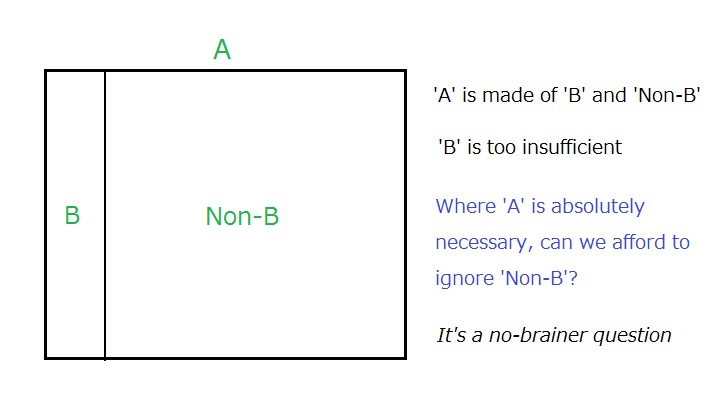
Hearing big players like Apple uttering ‘cryptographic keys’, many people might well automatically feel safe. However, the fact is the addition of cryptographic keys does not make up for the absence of passwords.
The outcome is a false sense of security; You feel as if you were safer when you are actually less safe. This could often be even more detrimental to safety than known absence of security.
Where we need solid security, we need to deploy a solid password for defending the cryptographic keys. Our observation is explicitly outlined here – “Removal of Passwords and Its Security Effect”
……………………..
Well, you might now ask “What can we do to solidly defend cryptographic keys by our secret credentials?
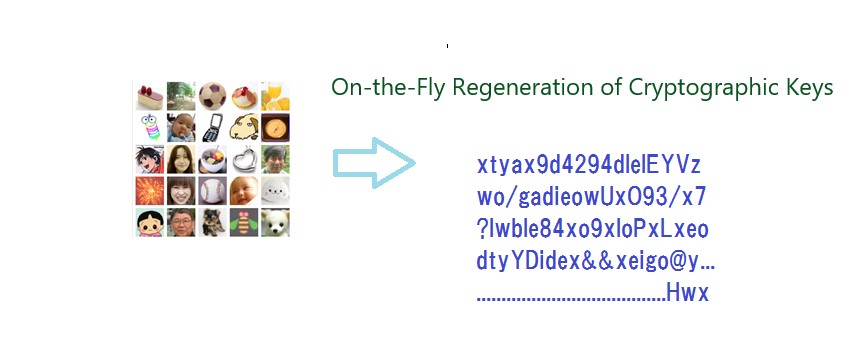
Our answer is to re-generate the keys from our episodic image memory on the fly as outlined here – “Try and experience the simulation of ‘On-the-fly Key Regeneration’ by yourself”
Key References
Account Recovery with Expanded Password System
For Achieving Solid Digital Identity on Information Security Buzz (Mar/2021)
What We Know for Certain about Authentication Factors
Digital Identity for Global Citizens
Image-to-Code Conversion by Expanded Password System
Summary and Brief History - Expanded Password System
Proposition on How to Build Sustainable Digital Identity Platform
Additional References
Removal of Passwords and Its Security Effect
Negative Security Effect of Biometrics Deployed in Cyberspace
External Body Features Viewed as ‘What We Are’
History, Current Status and Future Scenarios of Expanded Password System
Update: Questions and Answers - Expanded Password System and Related Issues
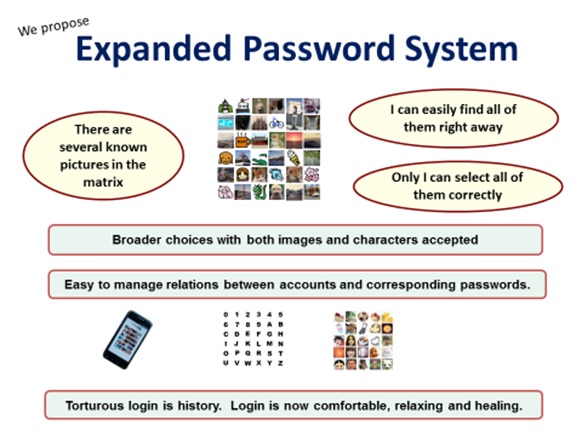
![“Expanded Password System
wane = Only I can select all of
BS] them correctly
Broader choices with both images and characters accepted
i
Easy to manage relenons between accounts and corresponding passwords.
&
Torturous login is history. Login is now comfortable, relaxing and healing
BO
250
08](https://contents.bebee.com/users/id/13855668/article/enjoy-a-comfortable-sense-of-C3kfLmCC5zM5/QO90N.jpeg)
< Videos on YouTube>
Slide: Outline of Expanded Password System (3minutes 2seconds)
Digital Identity for Global Citizens (10minutes - narrated)
Demo: Simplified Operation on Smartphone for consumers (1m41s)
Demo: High-Security Operation on PC for managers (4m28s)
Demo: Simple capture and registration of pictures by users (1m26s)
Slide: Biometrics in Cyber Space - "below-one" factor authentication
.
Articles from Hitoshi Kokumai
View blog
Taken up today is this TechRepublic report on voice print as a new password - https://www.techrepubl ...

I would like to take up this somewhat puzzling report - “Google advises passwords are good, spear ph ...

Another topic for today is “Passwordless made simple with user empowerment” · https://www.securitym ...
Related professionals
You may be interested in these jobs
-
Senior Manager
Found in: Jooble UK O C2 - 5 days ago
Glasgow Caledonian University Glasgow, United KingdomGlasgow Caledonian - the largest and leading modern university in Scotland - is a vibrant, values-led university with campuses in the heart of Glasgow and London. With a strong commitment to high quality education and research which supports the communities we serve, we have stro ...
-
Software Developer
Found in: Jooble UK O C2 - 17 hours ago
Manpower Group (UK) England, United KingdomYour role will be to create, develop and maintain the software running both on the Orion and on the Cloud analytics servers. You will be working with our Data Scientists to integrate advanced atmospheric modelling solutions, with our field teams to streamline and optimise the sen ...
-
Property Administrator
Found in: Jooble UK O C2 - 3 days ago
Hexagon Group Birling, Kent, United KingdomProperty Manager - Block Management · Eastbourne · £27,000 - £30,000 · We are working with a boutique-chartered surveying practice, who are looking to add a Block Property Manager to their growing block property management team. You will be joining an organisation that aspires to ...


&v=024)

Comments
Hitoshi Kokumai
2 years ago #2
Some people, perhaps with Apple included, are just indifferent to whether two authenticators are used in a security-enhancing ‘two-layer’ deployment or in a security- lowering ‘two-entrance’ deployment. Those people would not hesitate to allege that the combination of (1) biometrics OR default pincode AND (2) asymmetric key pairs provides a higher security than the combination of (1) pincode AND (2) key pairs, although the fact is the opposite.
Zacharias 🐝 Voulgaris
2 years ago #1
I've heard of biometrics as a token-based authentication mechanism, but I didn't think anyone would actually use it instead of passwords, on a device that's this vulnerable (according to a certain CS expert anyway, who lives in exile still). Whatever happened to 2-factor authentication?