How to Eliminate ‘Bad Password’

“Is passwordless authentication actually the way to go?” https://techhq.com/2021/05/is-passwordless-authentication-actually-the-way-to-go/
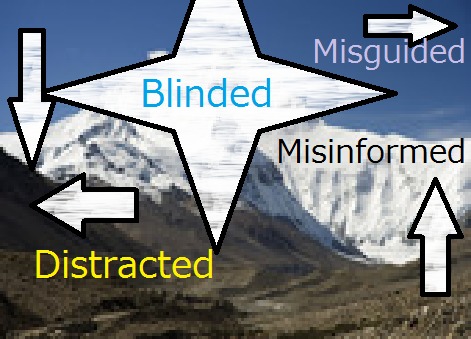
This report says “Experts reckon that passwords are no longer a secure method of identity verification.” I would like to follow it with “We should guard against ‘experts who are touting passwordless schemes.’
The password predicament will never go away however loudly we keep shouting ‘Bad passwords are bad.”, while attempting to eliminate the whole password family would only bring disaster in identity security.
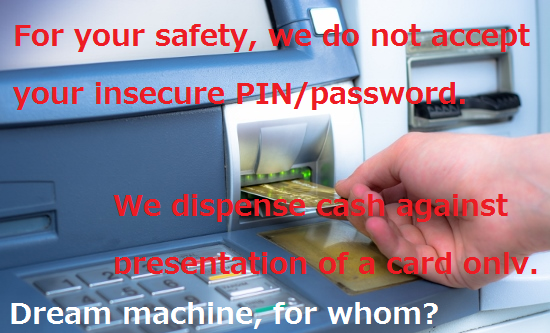
For eliminating ‘bad passwords’, we have only one valid choice – Find ‘good passwords.’
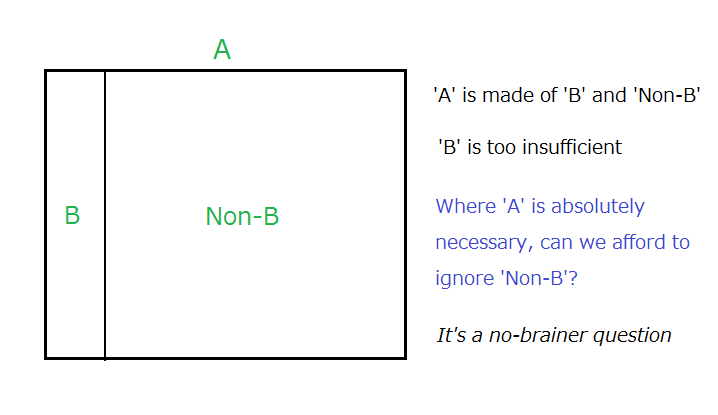
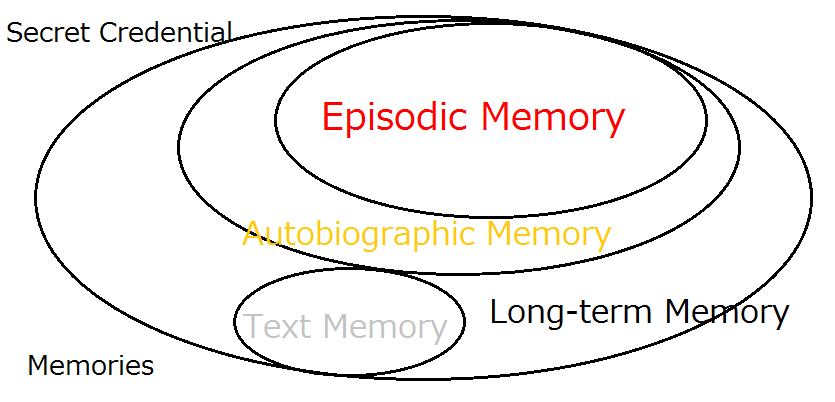
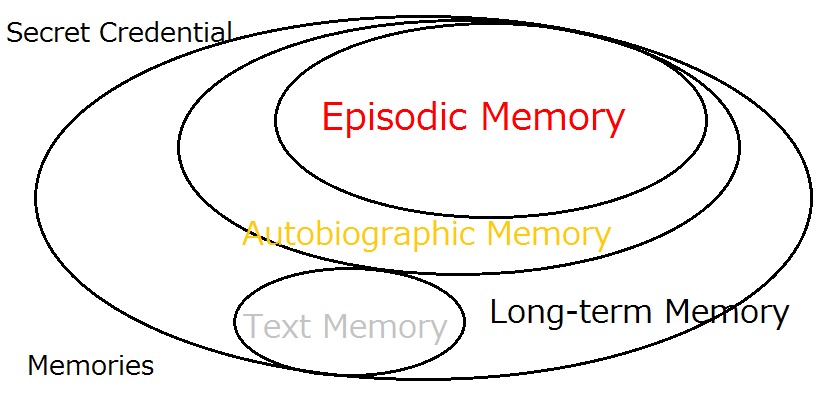
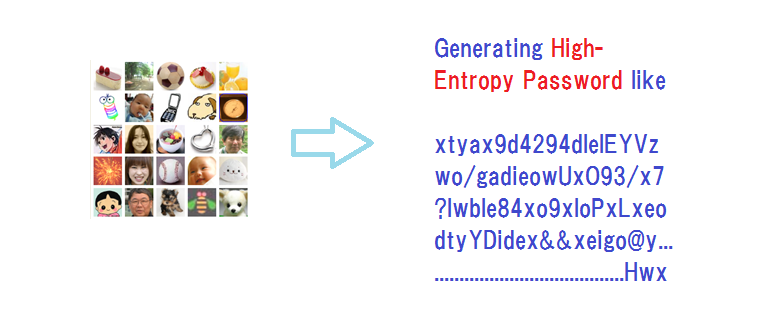
What we propose is look into ‘Non-text secret credentials
** Refutations will certainly be very welcomed.
Key References
“What we need to do for NOT achieving Solid Digital Identity”
Removal of Passwords and Its Security Effect
Negative Security Effect of Biometrics Deployed in Cyberspace
External Body Features Viewed as ‘What We Are’
Additional References
For Achieving Solid Digital Identity on Information Security Buzz (Mar/2021)
What We Know for Certain about Authentication Factors
Digital Identity for Global Citizens
Image-to-Code Conversion by Expanded Password System
Summary and Brief History - Expanded Password System
Proposition on How to Build Sustainable Digital Identity Platform
Account Recovery with Expanded Password System
History, Current Status and Future Scenarios of Expanded Password System
Update: Questions and Answers - Expanded Password System and Related Issues
< Videos on YouTube>
Slide: Outline of Expanded Password System (3minutes 2seconds)
Digital Identity for Global Citizens (10minutes - narrated)
Demo: Simplified Operation on Smartphone for consumers (1m41s)
Demo: High-Security Operation on PC for managers (4m28s)
Demo: Simple capture and registration of pictures by users (1m26s)
Slide: Biometrics in Cyber Space - "below-one" factor authentication

Articles from Hitoshi Kokumai
View blog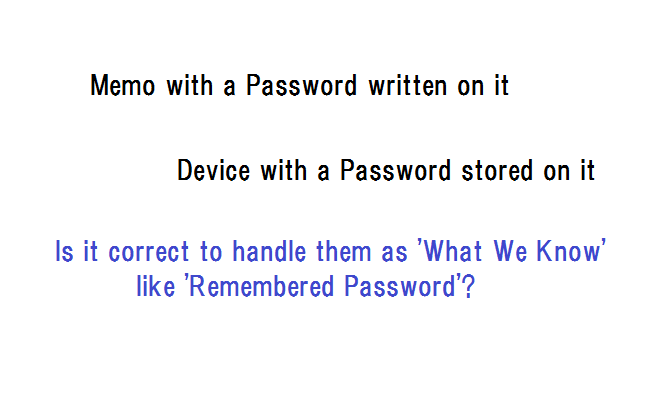
I got interested in this article -on the password problem · “Tech Q&A” · https://www.unionleader.c ...

Another topic for today is “Passwordless made simple with user empowerment” · https://www.securitym ...
We’ve come up with a slide presentation for “Bring a healthy second life to your legacy password sys ...
You may be interested in these jobs
-
Long Term Year 2 Teacher
Found in: Jooble UK O C2 - 5 days ago
Aspire People Kenilworth, Warwickshire, United KingdomAspire People is currently seeking a qualified and experienced Year 2 Teacher to join a vibrant school community in Kenilworth, Warwickshire This is a full-time position, available through Aspire People, a leading education recruitment agency. · Create a positive and inclusive le ...
-
BIM Technician
Found in: Jooble UK O C2 - 4 days ago
Energi People Woking, Surrey, United KingdomOur Client, a Building Services Design Consultancy is currently looking for a Revit MEP Technician on permanent bases. · The company has a wide and interesting project portfolio, including residential, commercial, educational, historical, industrial, leisure, marine, health and ...
-

Exterior Project Engineer
Found in: YadaJobs UK C2 - 1 week ago
Contechs Chelmsford, United KingdomOrder Ref: 56009 · Do you have the skills to fill this role Read the complete details below, and make your application today. · Position Title: Exterior Project Engineer · Duration: 10 Month Rolling Contract · Location: Dunton, Essex · Division: Product Development · Position D ...

Comments