Step-by-Step Analysis of Why and How Biometrics Brings Down Security
This is a follow-up of my earlier post – “Reality that so many security experts opt to not speak”
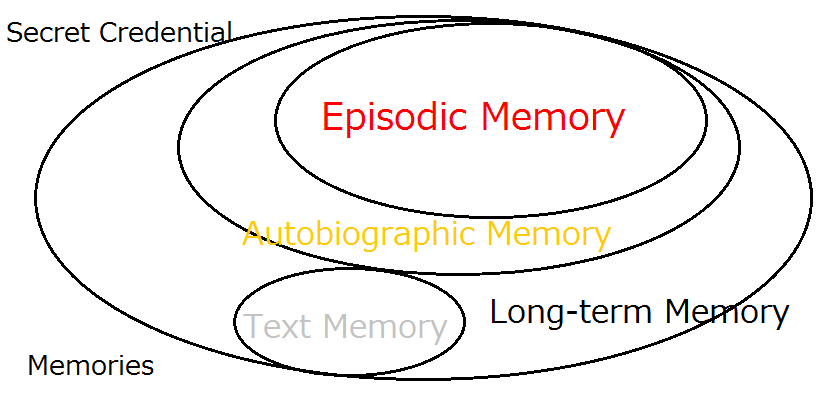
- Biometrics is probabilistic; it measures unpredictably variable body features of living animals in ever changing environments.
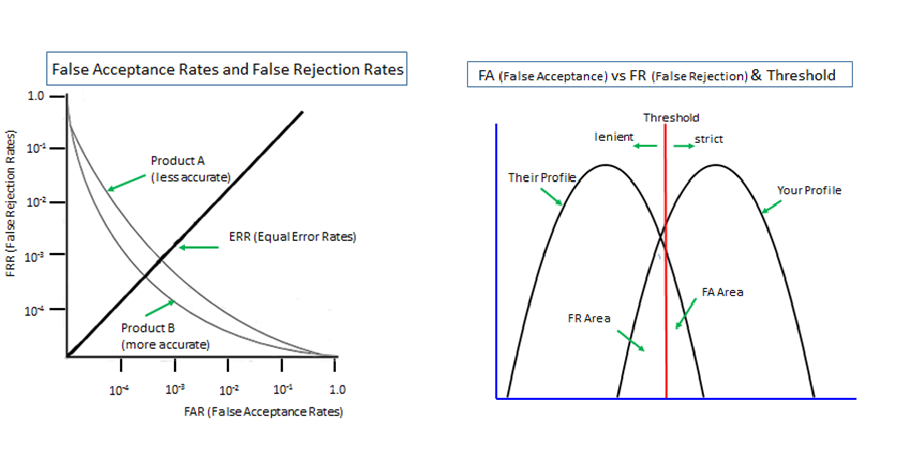
- Therefore, biometrics does not escape the trade-off between False Acceptance (False Match/False Positive) and False Rejection (False Non-Match/False Negative), outline of which is shown in the graphs above.
- The presence of False Rejection forces a fallback measure to be pr-provided in case the correct user gets rejected.
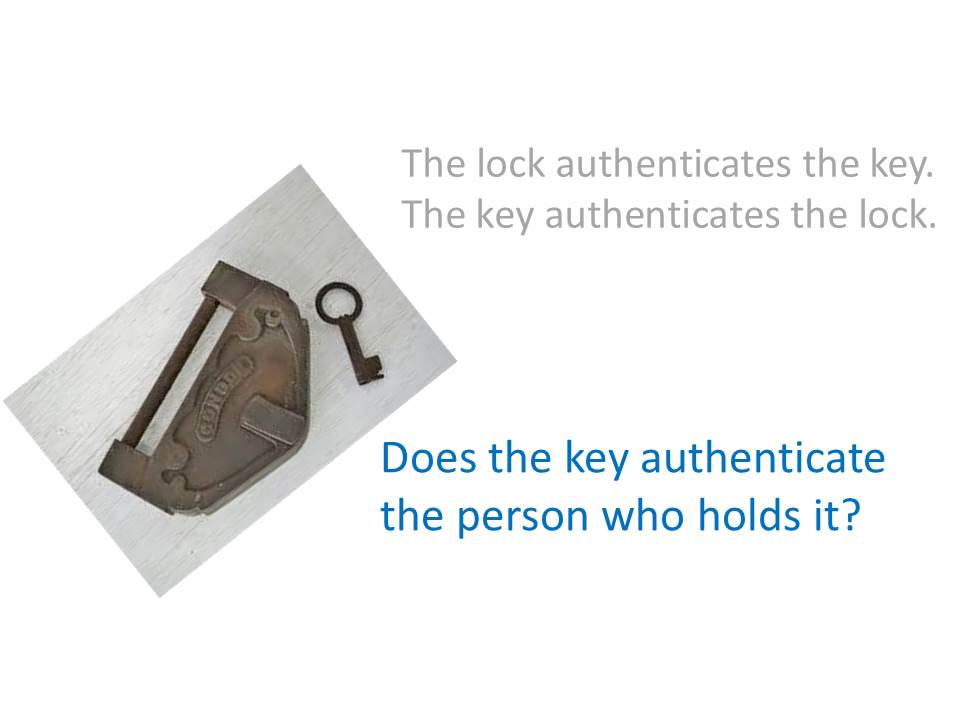
- Biometrics and a fallback measure need to be used together in a ‘multi-entrance’ deployment, as against a ‘multi-layer’ deployment. The former increases the attack surface (= brings down defense), while the latter decreases it (=brings up defense).
- Unless a default password/PIN is invalidated not to work as a fallback measure (with availability sacrificed), the overall security is lower than that of the default password/PIN used on its own.
As such, it is not that biometrics is not so secure as it claims to be, but that biometrics destroys the defense which a default password/PIN has otherwise provided.
Key References
“What we need to do for NOT achieving Solid Digital Identity”
Removal of Passwords and Its Security Effect
Negative Security Effect of Biometrics Deployed in Cyberspace
External Body Features Viewed as ‘What We Are’
Additional References
For Achieving Solid Digital Identity on Information Security Buzz (Mar/2021)
What We Know for Certain about Authentication Factors
Digital Identity for Global Citizens
Image-to-Code Conversion by Expanded Password System
Summary and Brief History - Expanded Password System
Proposition on How to Build Sustainable Digital Identity Platform
Account Recovery with Expanded Password System
History, Current Status and Future Scenarios of Expanded Password System
Update: Questions and Answers - Expanded Password System and Related Issues
![“Expanded Password System
wane = Only I can select all of
BS] them correctly
Broader choices with both images and characters accepted
i
Easy to manage relenons between accounts and corresponding passwords.
&
Torturous login is history. Login is now comfortable, relaxing and healing
BO
250
08](https://contents.bebee.com/users/id/13855668/article/step-by-step-analysis-of-tfhw6j0LKS4t/kwP3E.jpeg)
< Videos on YouTube>
Slide: Outline of Expanded Password System (3minutes 2seconds)
Digital Identity for Global Citizens (10minutes - narrated)
Demo: Simplified Operation on Smartphone for consumers (1m41s)
Demo: High-Security Operation on PC for managers (4m28s)
Demo: Simple capture and registration of pictures by users (1m26s)
Slide: Biometrics in Cyber Space - "below-one" factor authentication
Articles from Hitoshi Kokumai
View blog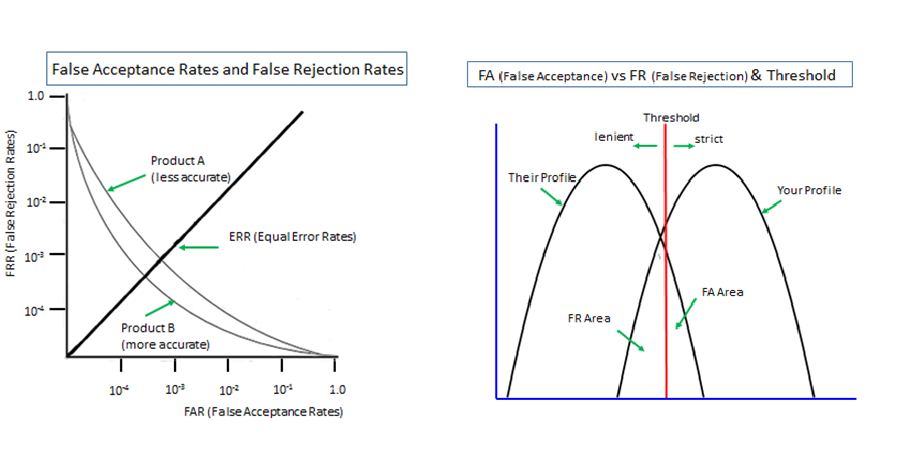
Biometrics is 'probabilistic' by nature since it measures unpredictably variable body features of li ...
There is actually a valid methodology that enable us to maximize the entropy of the secret credentia ...
Today's topic is this report - “How blockchain technology can create secure digital identities” · h ...
You may be interested in these jobs
-

Project Controls Lead
Found in: Appcast UK GBP C2 - 20 hours ago
Morson Group London, United KingdomWe are currently looking for a Project Controls Lead for our client on a permanent basis. This is to work on a large nuclear construction project in Suffolk. As the Project Controls Lead the role requires you to show experience in direction, delivery performance, leadership, exce ...
-
Commercial Gas Engineer
Found in: Jooble UK O C2 - 5 days ago
Phosters FM Watford, Hertfordshire, United KingdomJob Description: · The Multi Skilled Commercial/Domestic Gas Engineer based in Watford and surrounding areas covering the South of the country is required by our very successful FM Business. This is a mobile role covering a number of sites across the Midlands. You will be expect ...
-

Commissioning Engineer
Found in: Jooble UK O C2 - 15 hours ago
Ganymede West Sussex, United KingdomCommissioning Engineer Location – West Sussex · Opportunity to join an ongoing water framework · Roles Available for MEICA Commissioning Engineers · The Commissioning Engineer will ensure the efficient delivery of the MEICA Installation and commissioning phases to meet (or imp ...
Comments