Torturous login is history
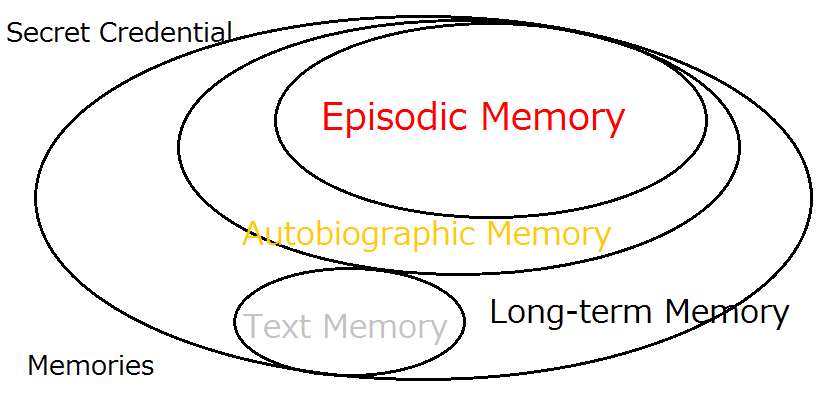
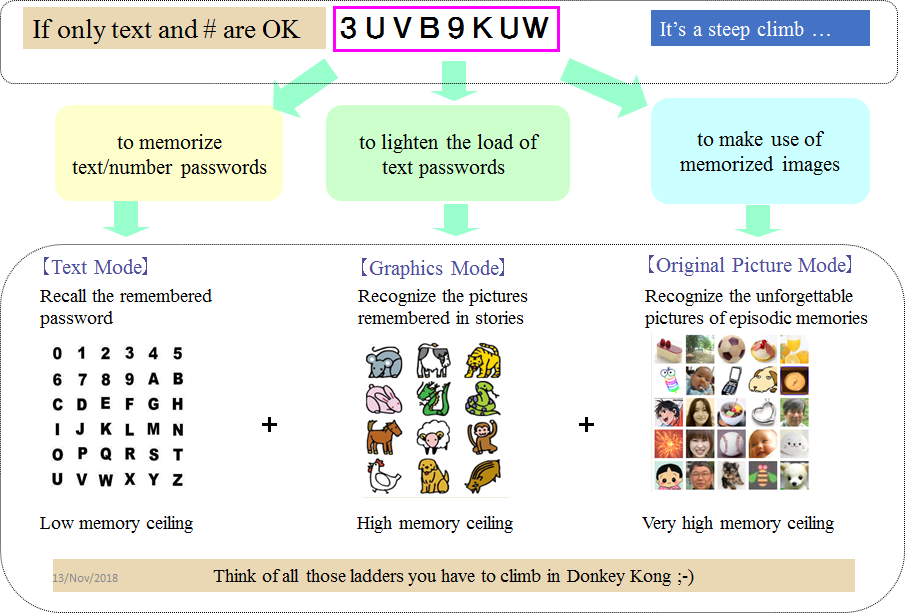
The login can now be joyful, healing and heartening with Expanded Password System that enables us to use our pleasant episodic image memory that had been acquired decades ago and solidly inscribed deep in our brain.
Images of toys, dolls, dogs and cats, for example, that our children used to love for years would jump into our eye even when we are placed in heavy pressure and caught in severe panic. It never fails to brings us joy and comfort.
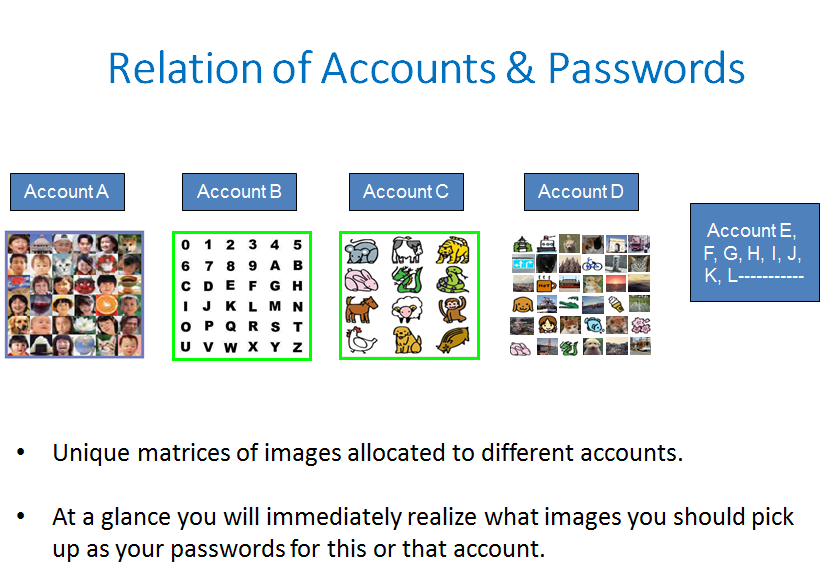
Furthermore, Expanded Password System brings us such desirable merits as
enabling us to manage dozens of different secret credentials effortlessly –https://www.linkedin.com/posts/hitoshikokumai_identity-authentication-password-activity-6794150779293982720-VZzH
reducing the burden of managing the correspondence between the accounts and the passwords – https://www.linkedin.com/posts/hitoshikokumai_identity-authentication-password-activity-6794149779996844032-LTU_
At our website, you can freely experience the on-the-fly re-generation of high-entropy text-passwords and cryptographic keys by Expanded Password System. https://www.mnemonicidentitysolutions.com/
![“Expanded Password System
wane = Only I can select all of
BS] them correctly
Broader choices with both images and characters accepted
i
Easy to manage relenons between accounts and corresponding passwords.
&
Torturous login is history. Login is now comfortable, relaxing and healing
BO
250
08](https://contents.bebee.com/users/id/13855668/article/torturous-login-is-history-4FD9ANXpwF4u/S3YSO.jpeg)
Key References
Account Recovery with Expanded Password System
For Achieving Solid Digital Identity on Information Security Buzz (Mar/2021)
What We Know for Certain about Authentication Factors
Digital Identity for Global Citizens
Image-to-Code Conversion by Expanded Password System
Summary and Brief History - Expanded Password System
Proposition on How to Build Sustainable Digital Identity Platform
Additional References
Removal of Passwords and Its Security Effect
Negative Security Effect of Biometrics Deployed in Cyberspace
External Body Features Viewed as ‘What We Are’
History, Current Status and Future Scenarios of Expanded Password System
Update: Questions and Answers - Expanded Password System and Related Issues
< Videos on YouTube>
Slide: Outline of Expanded Password System (3minutes 2seconds)
Digital Identity for Global Citizens (10minutes - narrated)
Demo: Simplified Operation on Smartphone for consumers (1m41s)
Demo: High-Security Operation on PC for managers (4m28s)
Demo: Simple capture and registration of pictures by users (1m26s)
Slide: Biometrics in Cyber Space - "below-one" factor authentication

Articles from Hitoshi Kokumai
View blog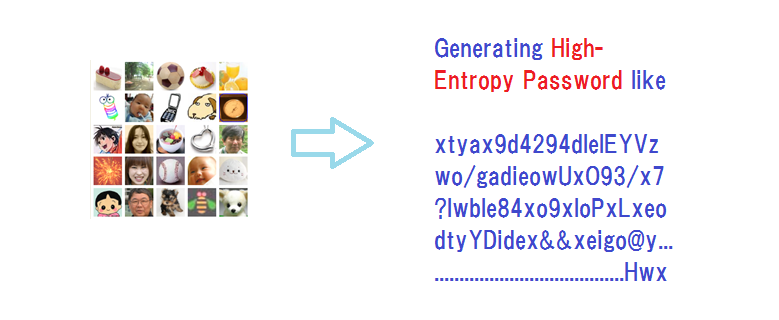
“Expanded Password System is no bad, but we do not need it. · We can rely on password managers that ...

Some friends directed my attention to this news report - · “Biometric auth bypassed using fingerpri ...
Biometrics is 'probabilistic' by nature since it measures unpredictably variable body features of li ...
You may be interested in these jobs
-

Finance Business Partner
Found in: beBee S2 UK - 2 days ago
Michael Page (UK) London, United Kingdom Full timeWe have been made aware of a global phishing campaign where employees from companies are being impersonated. We are confident that no PageGroup system has been breached. Find out how to protect yourself Opportunity to join a global, commercial oriented charity · Option to go perm ...
-
Senior Marketing Manager, Northern Europe
Found in: Jooble UK O C2 - 3 days ago
Insider London, United KingdomBefore jumping in on all the information about the role and what you can bring to the table, let us introduce ourselves real quick. · About us · Hi there We are Insider, a B2B SaaS company that drives growth for its clients around the world. How are we achieving this? We are co ...
-
AI Pharmaceutical Product Manager
Found in: Jooble UK O C2 - 1 week ago
Keller Executive Search London, United KingdomThis job is brought to you by Jobs/Redefined, the UK's leading over-50s age inclusive jobs board. · As an AI Product Manager, you will be responsible for the end-to-end management of AI-centric products, from conceptualization through to launch and beyond. You will work closely ...


Comments