Website Ready for Global Promotion of Expanded Password System

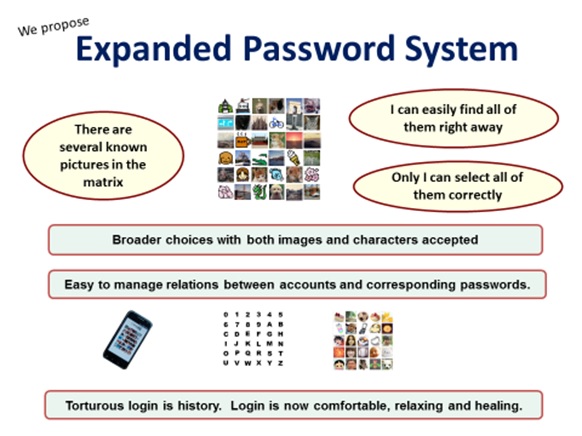
Our corporate website is ready for Mnemonic Identity Solutions Limited that we registered last August in UK as the headquarters for global promotion of Expanded Password System (EPS)
The website https://www.mnemonicidentitysolutions.com/ provides the trial course with which anyone can freely try and experience the flow of Image-to-Code Conversion by EPS; Pick up 3 to 6 images and you will see a high-entropy code generated from the sum of identifier data of the images you picked up. Select the same set of images and you will see the same code re-generated. This high-entropy code could be used as a very strong password or a mighty seed of cryptographic key.
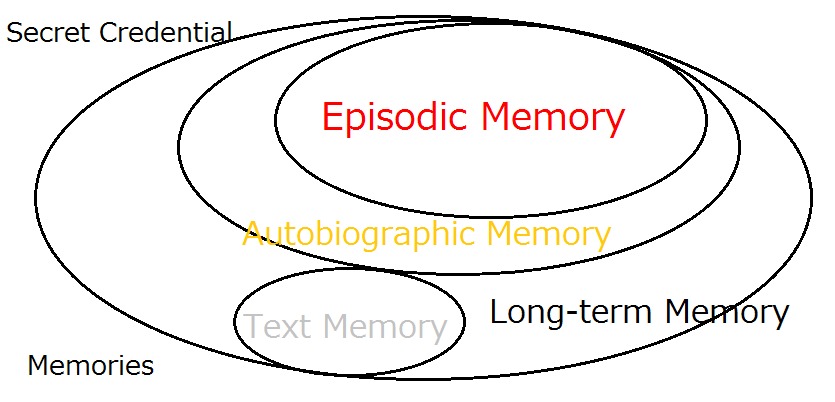
Assume that you had embedded and selected your ‘hard-to-forget’ and ‘panic-proof’ images of your episodic memory that had been solidly inscribed in your brain for years or decades and you will easily realize why EPS is deployed for national defense in Japan; it has been used since 2013, with the number of users increasing more than 10-fold over the 8 years.
Please do try and experience the trial course; you might well be inspired to think of a lot of practical use cases for solid security and/or friendly useability.
Key References
Account Recovery with Expanded Password System
For Achieving Solid Digital Identity on Information Security Buzz (Mar/2021)
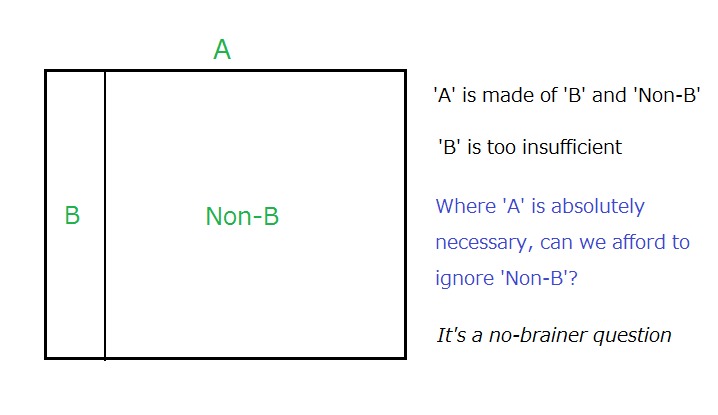
What We Know for Certain about Authentication Factors
Digital Identity for Global Citizens
Image-to-Code Conversion by Expanded Password System
Summary and Brief History - Expanded Password System
Proposition on How to Build Sustainable Digital Identity Platform
Additional References
Removal of Passwords and Its Security Effect
Negative Security Effect of Biometrics Deployed in Cyberspace
External Body Features Viewed as ‘What We Are’
History, Current Status and Future Scenarios of Expanded Password System
Update: Questions and Answers - Expanded Password System and Related Issues
< Videos on YouTube>
Slide: Outline of Expanded Password System (3minutes 2seconds)
Digital Identity for Global Citizens (10minutes - narrated)
Demo: Simplified Operation on Smartphone for consumers (1m41s)
Demo: High-Security Operation on PC for managers (4m28s)
Demo: Simple capture and registration of pictures by users (1m26s)
Slide: Biometrics in Cyber Space - "below-one" factor authentication
.
Articles from Hitoshi Kokumai
View blog
Today's topic is “Microsoft Exchange Autodiscover protocol found leaking hundreds of thousands of cr ...

Some friends directed my attention to this news report - · “Biometric auth bypassed using fingerpri ...
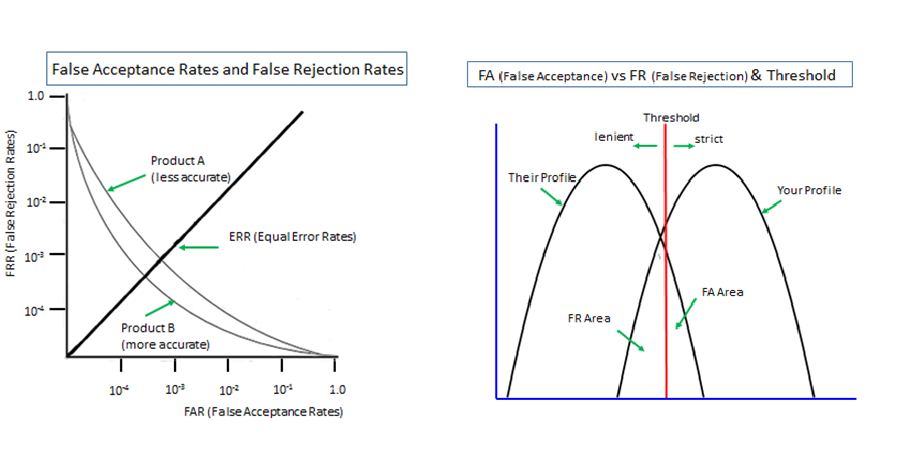
Biometrics is 'probabilistic' by nature since it measures unpredictably variable body features of li ...
Related professionals
You may be interested in these jobs
-
Senior Property Manager
Found in: Appcast UK C C2 - 3 days ago
Alder King Property Consultants City Of Bristol, United KingdomEXPERTISE. PARTNERSHIP. RESULTS. · These are the foundations on which Alder King has built its reputation over the past 100 years. · Today, we are a progressive and successful top 25 UK property consultancy, working with clients locally, regionally and nationally, adding value at ...
-

Audit/Audit Senior
Found in: Jooble UK O C2 - 3 days ago
UHY Hacker Young Group Chester, Cheshire, United KingdomWe live and breathe our core values and behaviours, and support our purpose of "Helping you Prosper". We are ambitious people, united in our mission to be exceptional auditors, accountants and business advisers delivering seamlessly integrated client service. · Through both our ...
-
Test Engineer
Found in: Jooble UK O C2 - 3 days ago
Vantage Consulting Aberdeen, United KingdomJob Description · The Role: · To support our expanding R&D team, we are looking to recruit a Test & Qualification Engineer. · Main Duties: · Develop and carry out testing of tools to satisfy client and industry standard qualification requirements. · Definition of qualificati ...


Comments
Zacharias 🐝 Voulgaris
2 years ago #1
Nice. BTW, I talk about the EPS, episodic memory, and various other aspects related to secure authentication protocols in my Authentication and Integrity Tools course I published recently. I am not affiliated with this initiative but see merit in it anyway, which is why I included it in my course. Cheers