Try and experience the simulation of ‘On-the-fly Key Regeneration’ by yourself
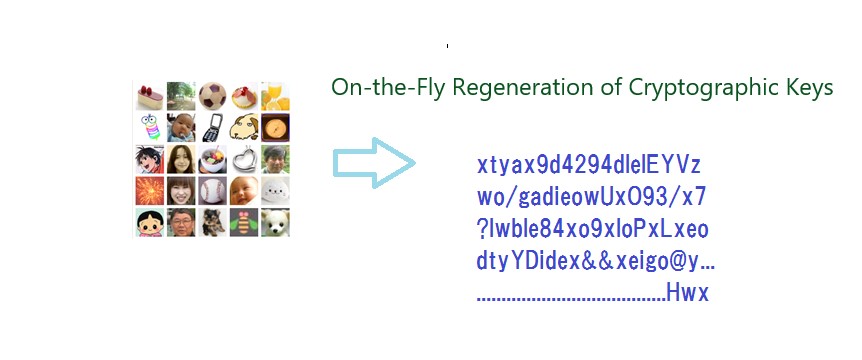
With the trial course of ‘Image-to-Code Conversion by Expanded Password System’ provided at our new website https://www.mnemonicidentitysolutions.com/, you can try a simulation of having cryptographic keys re-generated on the fly from your image memory.
Select the same images again and notice the same code is generated, even when the images are shuffled, the same code is generated for the same set of images. This high-entropy code could be used as a mighty seed of cryptographic key. Imagine that a key opens a digital lock, the key is never stored *anywhere*, it is generated on each invocation.
More information is provided in this article - “Account Recovery with Expanded Password System” https://www.linkedin.com/pulse/account-recovery-expanded-password-system-hitoshi-kokumai/
Incidentally, besides the new corporate website, we now have our company page on LinkedIn at https://www.linkedin.com/company/mnemonic-identity-solutions-limited/
![“Expanded Password System
wane = Only I can select all of
BS] them correctly
Broader choices with both images and characters accepted
i
Easy to manage relenons between accounts and corresponding passwords.
&
Torturous login is history. Login is now comfortable, relaxing and healing
BO
250
08](https://contents.bebee.com/users/id/13855668/article/try-and-experience-the-simulation-5ut91PoquD6r/4Wxdo.jpeg)
Key References
Account Recovery with Expanded Password System
For Achieving Solid Digital Identity on Information Security Buzz (Mar/2021)
What We Know for Certain about Authentication Factors
Digital Identity for Global Citizens
Image-to-Code Conversion by Expanded Password System
Summary and Brief History - Expanded Password System
Proposition on How to Build Sustainable Digital Identity Platform
Additional References
Removal of Passwords and Its Security Effect
Negative Security Effect of Biometrics Deployed in Cyberspace
External Body Features Viewed as ‘What We Are’
History, Current Status and Future Scenarios of Expanded Password System
Update: Questions and Answers - Expanded Password System and Related Issues
< Videos on YouTube>
Slide: Outline of Expanded Password System (3minutes 2seconds)
Digital Identity for Global Citizens (10minutes - narrated)
Demo: Simplified Operation on Smartphone for consumers (1m41s)
Demo: High-Security Operation on PC for managers (4m28s)
Demo: Simple capture and registration of pictures by users (1m26s)
Slide: Biometrics in Cyber Space - "below-one" factor authentication
Articles from Hitoshi Kokumai
View blog
Some friends directed my attention to this news report - · “Biometric auth bypassed using fingerpri ...
Bad guys, who have a quantum computer at hand, would still have to break the part of user authentica ...

Today's topic is “Microsoft Exchange Autodiscover protocol found leaking hundreds of thousands of cr ...
Related professionals
You may be interested in these jobs
-
Automotive Test Engineer
Found in: Jooble UK O L C2 - 5 days ago
Service Care Solutions Buckingham, Buckinghamshire, United KingdomAutomotive Test Engineer k - on-site BirminghamWe are currently looking for a passionate, talented and experienced Quality Assurance Test Engineer to join a fantastic tech driven company based in Birmingham. This is an incredible opportunity to work for one of the most dynamic sm ...
-
Senior Software Back-End Engineer
Found in: Talent UK C2 - 1 day ago
TP ICAP Belfast, United Kingdom Full timeRole Overview · As a Senior Back-End Software Engineer at TP ICAP you will be part of a talented team delivering business critical software for the internal broking division and their external customer base. You will work within an Agile environment, from design through to imple ...
-
Senior Liferay DXP Software Developer
Found in: Jooble UK O C2 - 1 day ago
Nexus Jobs Limited Norwich, Norfolk, United KingdomSenior Liferay DXP Software Developer - Norwich · Job Description · Senior Liferay DXP Software Developer We urgently require a Senior Liferay DXP Software Developer with at least 3 to 5 years expertise of working Liferay and Java. The project involves a Liferay DXP Upgrade. Yo ...



Comments
Zacharias 🐝 Voulgaris
2 years ago #1
Man, if you were to work with us on this stuff, the world would experience a renaissance in Cybersecurity…